cert-manager自动颁发证书
cert-manager简介
cert-manager 是一个云原生证书管理开源项目,用于在 Kubernetes 集群中自动管理和颁发来自各种颁发源的 TLS 证书,它可以从各种受支持的来源颁发证书,包括 Let’s Encrypt、HashiCorp Vault和Venafi以及私有 PKI,它将确保证书定期有效和更新,并在到期前的适当时间尝试更新证书。
k8s集群中安装cert-manager
参考:Installation - cert-manager Documentation
推荐使用helm chart进行安装:
helm repo add jetstack https://charts.jetstack.iohelm repo updatekubectl apply -f https://github.com/cert-manager/cert-manager/releases/download/v1.13.0/cert-manager.crds.yamlhelm install \ cert-manager jetstack/cert-manager \ --namespace cert-manager \ --create-namespace \ --version v1.13.0 \ # --set installCRDs=true为nginx-ingress自动签发证书
使用CA
这里使用一个官方的示例,但略有不同:
selfsigned-cert.yaml
apiVersion: cert-manager.io/v1kind: ClusterIssuermetadata: name: selfsigned-cluster-issuerspec: selfSigned: {}---apiVersion: cert-manager.io/v1kind: Certificatemetadata: name: selfsigned-ca namespace: cert-managerspec: isCA: true commonName: ca.nblh.local subject: countries: - CN localities: - HangZhou organizationalUnits: - Root CA organizations: - nblh.local postalCodes: - "310000" provinces: - ZheJiang streetAddresses: - fandou graden serialNumber: SELF20230919 duration: 43800h secretName: selfsigned-ca-secret privateKey: algorithm: ECDSA size: 256 issuerRef: name: selfsigned-cluster-issuer kind: ClusterIssuer group: cert-manager.io
---apiVersion: cert-manager.io/v1kind: ClusterIssuermetadata: name: cluster-ca-issuerspec: ca: secretName: selfsigned-ca-secret---# 手动签发证书# apiVersion: cert-manager.io/v1# kind: Certificate# metadata:# name: kuard-tls# namespace: test# spec:# dnsNames:# - kuard.nblh.local# - w1.nblh.local# issuerRef:# group: cert-manager.io# kind: ClusterIssuer# name: selfsigned-cluster-issuer# secretName: kuard-tls# duration: 87600h# usages:# - digital signature# - key enciphermentkuard-deploy.yaml
apiVersion: v1kind: Servicemetadata: name: kuard namespace: testspec: ports: - port: 80 targetPort: 8080 protocol: TCP selector: app: kuard---apiVersion: apps/v1kind: Deploymentmetadata: name: kuard namespace: testspec: selector: matchLabels: app: kuard replicas: 1 template: metadata: labels: app: kuard spec: containers: - image: gcr.io/kuar-demo/kuard-amd64:blue imagePullPolicy: IfNotPresent name: kuard ports: - containerPort: 8080kuard-ingress.yaml
apiVersion: networking.k8s.io/v1kind: Ingressmetadata: name: kuard annotations: cert-manager.io/cluster-issuer: "cluster-ca-issuer"spec: ingressClassName: nginx tls: - hosts: - kuard.nblh.local - w1.nblh.local secretName: kuard-tls rules: - host: kuard.nblh.local http: paths: - path: / pathType: Prefix backend: service: name: kuard port: number: 80应用清单文件创建证书:
kubectl apply -f kuard-deploy.yaml -f selfsigned-cert.yaml -f kuard-ingress.yaml# 创建完成之后使用以下命令查看证书颁发状态,READY为True则表示已颁发kubectl get certificate -ANAMESPACE NAME READY SECRET AGEcert-manager selfsigned-ca True selfsigned-ca-secret 9stest kuard-tls True kuard-tls 3s导出证书文件安装到操作系统或者浏览器当中:
kubectl get secrets kuard-tls -ojsonpath='{.data.tls\.crt}' | base64 -d > tls.crtMacOS钥匙串中选择始终信任:

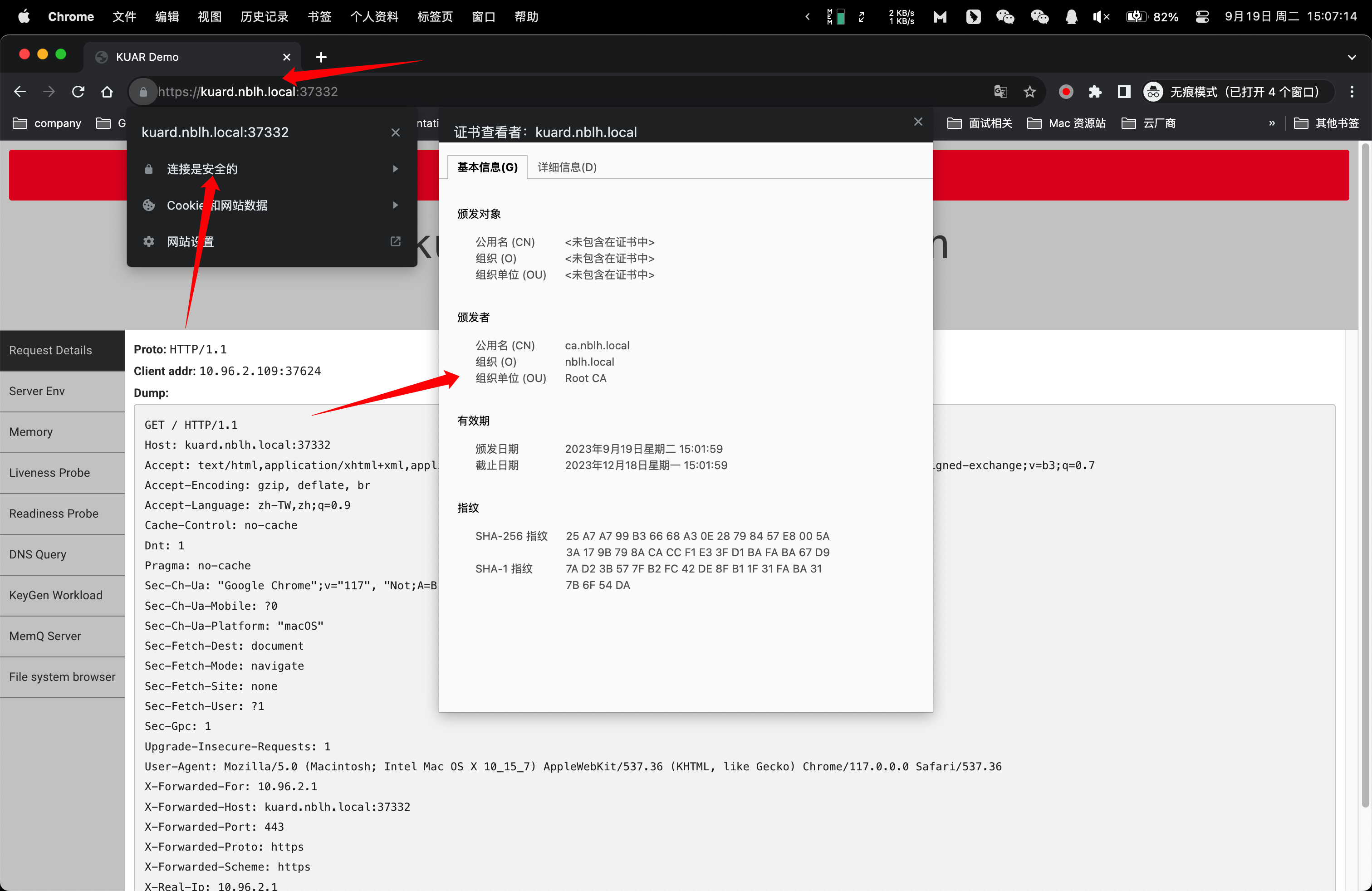
打开浏览器直接访问,可以看到自签证书已经可以正常使用:
直接签发
selfsigned-cert.yaml
apiVersion: cert-manager.io/v1kind: Issuermetadata: name: selfsigned-issuer namespace: testspec: selfSigned: {}---apiVersion: cert-manager.io/v1kind: Certificatemetadata: name: selfsigned-certspec: dnsNames: - kuard.nblh.local secretName: selfsigned-cert-tls issuerRef: name: selfsigned-issuerkuard-ingress.yaml
apiVersion: networking.k8s.io/v1kind: Ingressmetadata: name: kuard annotations: cert-manager.io/issuer: "selfsigned-issuer" # 与上面的issuer对应spec: ingressClassName: nginx tls: - hosts: - kuard.nblh.local - w1.nblh.local secretName: selfsigned-cert-tls # 与上面的secret对应 rules: - host: kuard.nblh.local http: paths: - path: / pathType: Prefix backend: service: name: kuard port: number: 80步骤和上面类似,就不在此赘述。
手动更新证书
kubectl edit certificate kuard-tls -n test# 在spec字段下添加以下两行 duration: 87600h # 10 years renewBefore: 720h # 30 days# 保存并退出
# 删除原来的secret,让certmanager重新自动生成secretkubectl get certificate kuard-tls -o=jsonpath='{.spec.secretName}' | xargs kubectl delete secret